Incident Response Team
All the Incident Response solutions have the support of a team of security analysts, responsible for receiving, triage, analyze and respond to all alerts generated, according to their criticality. They decide all actions to be taken, including recovery actions. This team works to maintain pre-established levels of availability, confidentiality and integrity, according to the environments and scenarios, focusing on functionality.
Firewall Monitoring
Companies are under constant pressure to protect critical systems and information, but many have failed in their security strategy for not keeping a robust system of monitoring logs. The Aser Security applies a monitoring methodology and management of logs sent in from our customers security infrastructure.
The response service incidents Firewall provides proactive assessment of suspicious activity through the equipment, while you manage the Firewall rules. The ASER along with the client defines the incident response plan and when an anomaly is detected, starts the sorting and fires escalation plan.
IDS / IPS Monitoring
The Aser Security offers its IRT (Incident Response Team) to manage the device IDS / IPS our customers. This mode fits for you who already have in your environment an IDS / IPS running and with internal management, but intends to expand the triage ability of the thousands of events that are generated. The Aser Security developed sensors that can capture events generated by our intrusion detection/prevention system, compress them and send them to our central security operations (SOC) for correlation and analysis by highly qualified staff.
The ASER along with the client, defines the response plan to incidents and when an attack is detected, starts the triage and fires the escalation plan.
WAF Monitoring
The WAF Monitoring and incident response service offers proactive assessment of suspicious activity while you manage the rules of the WAF. The ASER along with the client defines the incident response plan and when an anomaly is detected, starts the triage proccess and fires the escalation plan.
An easy and affordable service that integrates the Web Application Firewall in one central, allowing DDoS mitigation and treatment of incidents in real time.
Traffic Monitoring (ITM)
ITM is essentially a network diagnostic tool. Its features are intended to provide to the network administrator information to permit this professional understand what your travels in each network routing point that instant, what the volume of traffic, what protocols that compose it, that the applications generate, which users these applications and provide input on the history of the network, if this behavior is recurrent or exception.
With this information the IT staff is able to anticipate problems and act proactively in pursuit of its resolution, or even plan inevitable extraordinary activities such as updgrades for operating system or antivirus, with minimal impact to the corporation’s activities, based prospects in reporting the usual behavior of traffic on your network.
From an administrative point of view, document the behavior of a communication network enables to measure their use and thus verify possible underutilisation of resources or anticipate the need for expansion and structural improvements, preventing emergencies that would lead to investments made without proper planning.

Links and Applications Monitoring
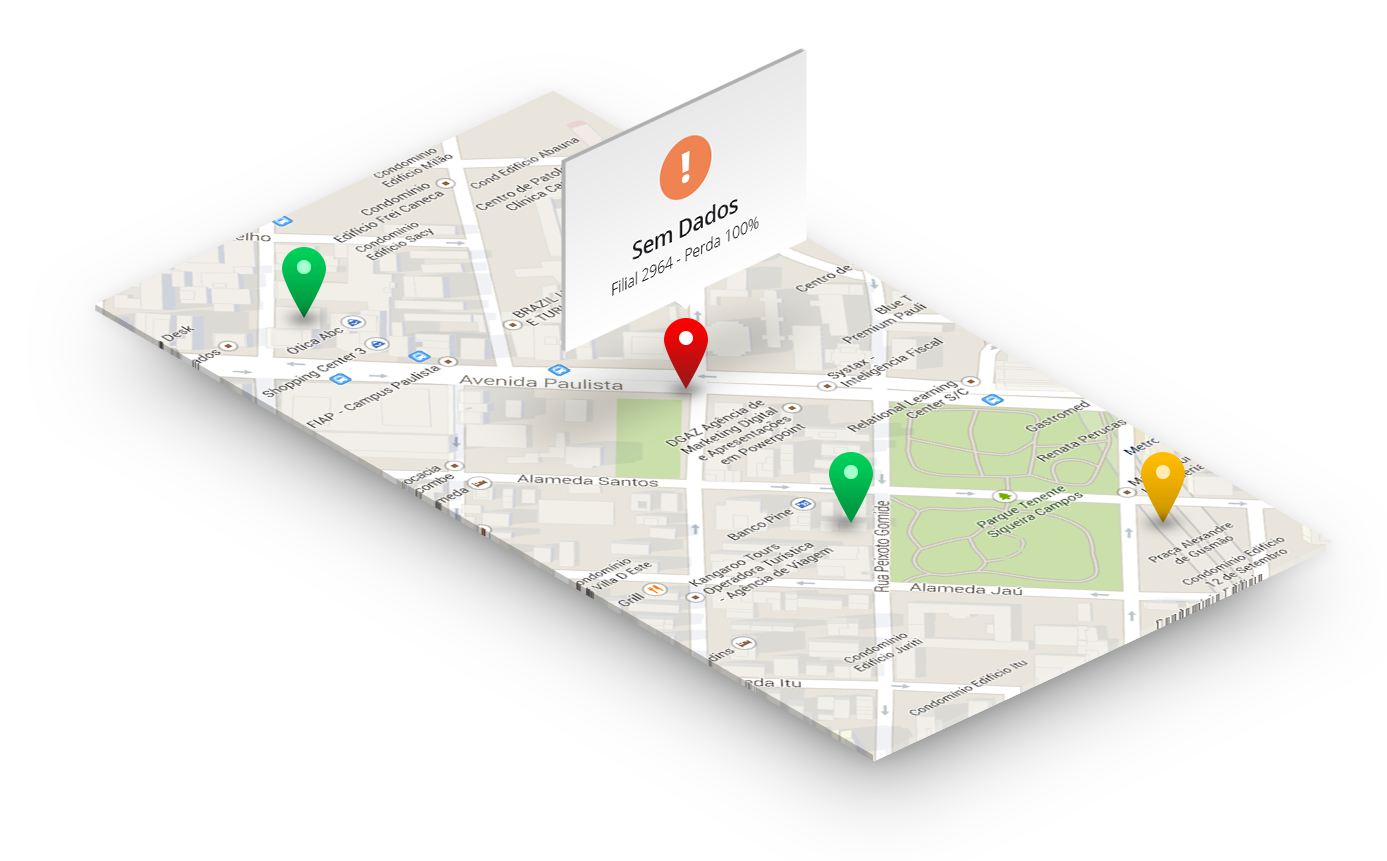
Displays maps with all points monitored in real time. Displays the status of the links and generate visual and audio alerts to the central Aser Security NOC. Detect packet loss and activation of redundant links. Generates accurate reports containing links behavior history, scoring all incidents, partial and total times of service interruption.